Since the development of SeaShell iOS post-exploitation framework started, I was thinking about evasion techniques that can be applicable to a non-jailbroken (or jailbroken but rootless) iOS systems. So, after few days of brainstorming I came with few ideas that can be used and that I have already implemented in SeaShell.
Persistence
Typically, we use launchctl to achieve persistence on iOS/macOS. However, on non-jailbroken iOS devices (and even on jailbroken ones nowadays, as they are rootless), the root directory (/) is not writable, which means that we cannot write to /Library/LaunchAgents or /Library/LaunchDaemons. Consequently, we are unable to install a .plist file that would launch the payload.
Recognizing the need for a persistence installation method, I came up with an idea: What if we inject the payload into existing user applications? Initially, I considered inserting a dynamic library (.dylib) into the bundle executable of an application, but this would require re-signing the binary. Then, I had another idea: we can replace the bundle executable with a custom binary that will first execute the payload and then call the original executable.
Essentially, our custom executable will use the posix_spawn() function to execute the payload and then use execve() to invoke the original executable. Since execve() replaces the current process image with a new one, this is the optimal approach to launch the application. Below, you can find a diagram illustrating this process using the Calculator.app as an example.
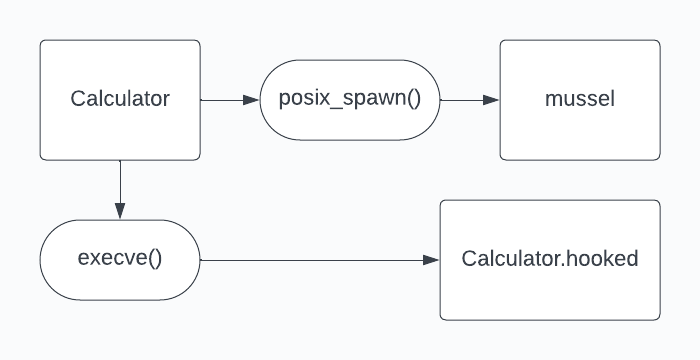
To perform hooking we need:
- 1. Patch
Info.plistand addCFBundleBase64Hashcontaining base64 representation of<host>:<port>to connect back to. - 2. Move
CalculatortoCalculator.hooked. (CFBundleExecutablefor other applications) - 3. Upload custom executable that will perform the loading and call it
Calculator(CFBundleExecutablefor other applications). - 4. Upload
musselpayload that will call Pwny and perform connection. - 5. Perform
chmodoperations on both custom executable andmussel, otherwiseposix_spawn()will die witherror 13which isPermission denied.
I am concerned that persistence can be called an evasion technique due to the fact that we are injecting our payload into another application infecting it.